Posts filed under ‘Privacy’
Money Smart Week® @Your Library (April 2-9, 2011) and ID Theft Resources
Posted by Robert J. Lackie
The American Library Association (ALA), the Federal Reserve, and I hope that many librarians and their libraries are participating in the first ever national Money Smart Week® @Your Library this week, April 2-9, 2011! Money Smart Week (a registered service mark of the Federal Reserve Bank of Chicago) events are taking place now at member libraries across the country covering topics from learning how to apply for a mortgage to teaching young people about credit to ID theft protection, with many resources uploaded to the Money Smart Week® @Your Library official site, linked above. Visit this site for information on this initiative and for news and important links you can use this week, right now!Additionally, Rider University’s Center for Business Forensics (CBF) has hosted several free interactive panel presentations for the general public (students, staff, community members, etc.) and law enforcement personnel focusing on the major issues surrounding identity theft—including financial literacy—and providing insight into the widespread, varying, and serious nature of identity theft.
Dr. Drew Procaccino, a professor of computer information systems at Rider, has organized and led these Identity Theft: What You Need to Know sessions with panels of experts from law enforcement, banking, legal, library, IT, CIS, and health care organizations. As a panelist several times and as a new member of the American Library Association’s Academic MSW@Your Library Committee, I want to again provide everyone with some frequently repeated “best practices” from the panel experts for detection and protection, especially since this week (until April 9, 2011), we are officially celebrating the 10th year anniversary of Money Smart Week. Here are the 10 best practices/advice from our panel of experts at Rider’s CBF sessions:1. Shred with a crosscut or micro shredder pieces of mail that contain any personal information before throwing them in the trash at home or at work.
2. Place outgoing mail and retrieve incoming mail via a locking mailbox or official Postal Service box.
3. Use a virtual credit card number (available through most banks) for online purchases, rather than your “real” credit card—connected to your card, the virtual number can be set up to only be used once, for that one online purchase (or for longer, but only if you wish).
4. Keep an eye on your credit card when you are paying for something—don’t allow it to disappear out of your sight (skimming of your card could occur).
5. Inventory/photocopy what is in your wallet/purse and place that photocopy (back and front of cards) in a locked cabinet—if your wallet/purse is stolen, you have all the info.
6. Never respond to an unsolicited email from your bank, medical organization, etc., and don’t unsubscribe—don’t even click on the link, just delete it.
7. Cover the ATM keypad from prying eyes and cameras with one hand while you enter your PIN.
8. Review your credit reports (you can get a free one each year from each of the three credit reporting agencies, and if you stagger requests, you can get one every four months).
9. Clear private data from your browser (i.e., Firefox, IE, or Safari): delete temporary files, browsing history, cookies, cache, saved form information, and saved passwords, especially when using a public computer or kiosk at a library, hotel, airport, coffee shop, etc., and then shut down your browser.
10. Use different passwords for different sites—and try changing/updating your passwords to passphrases.
Last but least, my annually-updated free website, Personal Profiles and Other Publicly Available Information: An Internet Hotlist on Detecting and Protecting Your Digital Footprint, contains some of my favorite ID theft protection, privacy information, and financial assistance sites, among other things, found on experts’ sites on the free Web, including our Identity Theft: What You Need to Know seminar project’s 29-page handout from Rider University, available to all.
Remember, according to Terri Cullen, author of The Wall Street Journal Complete Identity Theft Guidebook: How to Protect Yourself from the Most Pervasive Crime in America, ( “…Identity theft covers several different specific crimes, and collectively,…is one of the easiest crimes to commit, one of the hardest to prosecute, and one that is drawing increasing attention from the media.” So, feel free to share this information with all of your patrons and students, especially because proactively protecting your digital footprint and your finances is much easier than dealing with them after the fact as a victim—being a victim can be a very emotional, time-consuming, and financially-unrewarding process. Again, prevent it from ever happening to you, and help others do the same.
Anyway, I hope this all helps you during Money Smart Week® @Your Library this week, April 2-9, 2011. Enjoy partnering with and/or sharing pertinent information from your community groups, financial institutions, government agencies, educational organizations, and other financial experts this week to help all of our consumers learn to better manage and protect their personal finances!-Robert
Balancing privacy and patron control of personal information.
A colleague and I were discussing the recent Facebook TOS kerfuffle and she said she was fascinated by how much privacy people are willing to give away in exchange for a desired experience. I agreed that I am equally fascinated, and that it is vitally important for librarians to be on the vanguard of monitoring these trends, and educating our customers as to the possible risks of sharing too much information.
But I also think that librarians, at times, can be too knee-jerk about privacy issues, and I wonder if while looking at one end of the Facebook dustup (big corporation trampling on privacy rights) we might be missing some important lessons on the other end (big corporation letting customers control their own information in exchange for a highly engaging experience. And Facebook DOES give customers a tremendous, leading edge, amount of control. See: “10 Privacy Settings Every Facebook User Should Know.)
We all know that people (myself, and probably you included) will share personal information in exchange for a quality experience. We share personal renting and buying habits in exchange for Netflix and Amazon recommendations. We share personal reading habits on GoodReads and LibraryThing to connect with others who share our interests and tastes. We share our credit card numbers with many online vendors in exchange for the convenience of “one-click” ordering.
We know all this, and we personally experience the benefits, but librarians still seem generally loathe to let our customers share their personal information in exchange for anything. We don’t just protect customer privacy, we paternalistically protect it from the customers themselves, rendering them childlike. Our privacy philosophy often reduces down to, “We know better”, or “You can’t be trusted with that–you’ll hurt yourself.”
 Our choice to disallow customer control of their own information means that their needs for connection and social networking go unmet, which in turn creates opportunities for entrepreneurial companies like Library Elf, GoodReads, and LibraryThing (created by frustrated library lovers, I wonder?) to come in and fill those needs. Which is great, but why aren’t libraries creating and offering these experiences?
Our choice to disallow customer control of their own information means that their needs for connection and social networking go unmet, which in turn creates opportunities for entrepreneurial companies like Library Elf, GoodReads, and LibraryThing (created by frustrated library lovers, I wonder?) to come in and fill those needs. Which is great, but why aren’t libraries creating and offering these experiences?
I worry every day about whether libraries will be relevant, three, five, or ten years from now. Unless we start allowing our customers to make decisions about their own personal data, AND start building systems that offer them a social networked experience based on their ability to selectively share their heretofore private info, I fear that libraries will grow increasingly irrelevant to our customers.
Detecting and Protecting your Digital Footprint: ID Theft and You–Yes, You!
 Back in December, I blogged about Making–and Protecting–your Digital Footprint: Do you Care? Even a Little Bit??, noting that even though I am online quite a bit, I still consider myself one of “The Concerned and Careful” type, especially concerning personal information available about myself and my family online and take steps to proactively limit and/or keep a watchful eye of our online data. As a previous victim of identity fraud, I must say that it changes your perspectives somewhat. Anyway, according to the very interesting and earlier-mentioned Pew Internet & American Life Project’s “Digital Footprints” report from last December, one in five online adults (21%) fall into this “Concerned and Careful” category, so I know that I am not standing alone.
Back in December, I blogged about Making–and Protecting–your Digital Footprint: Do you Care? Even a Little Bit??, noting that even though I am online quite a bit, I still consider myself one of “The Concerned and Careful” type, especially concerning personal information available about myself and my family online and take steps to proactively limit and/or keep a watchful eye of our online data. As a previous victim of identity fraud, I must say that it changes your perspectives somewhat. Anyway, according to the very interesting and earlier-mentioned Pew Internet & American Life Project’s “Digital Footprints” report from last December, one in five online adults (21%) fall into this “Concerned and Careful” category, so I know that I am not standing alone.
Well, I said in my earlier post that I would return to this topic, and I do so today because of two reasons: one, I just read my fellow Library Garden blogger and friend Amy Kearns’ funny and enlightening Facebook post yesterday about our “digital” and “real” lives colliding, and about me stalking her in Princeton (OK, she was only joking about the stalking part–no really, she was joking). I have to say that, because since showing a journalist during an interview how easy I could find info on her, she quoted me in her US1 article when I jokingly said, “Now I can stalk you.” (note that the link to my Feb. 2008 website on this topic is included, but the article accidentally hyperlinked a period at the end of the sentence, so remove the period from the URL — it should be http://www.kn.sbc.com/wired/fil/pages/liststudentpe3.html (Personal Profiles and Other Publicly Available Information: An Internet Hotlist on Detecting and Protecting Your Digital Footprint)
Second reason to return to this topic: Rider University’s Center for Business Forensics hosted a free seminar focusing on the major issues surrounding identity theft and fraud, offering to the public insight into the widespread, varying, and serious nature of identity theft. It was well attended and there were a lot of questions, especially since the expert panel consisted of detectives, a VP in banking, and professor in health information management, and my good friend–and Rider’s very own web expert, blogger, and manager of information technology–John LeMasney, who, incidentally, already placed his April Google Docs presentation online for us (another detective also joined the panel not originally listed on the website advertisement, Detective Tracy McKeown, and Investigator Bethany Schussler was unable to make it). This seminar was led by Dr. J. Drew Procaccino, Associate Professor of Computer Information Systems, who has researched identity theft, biometrics and smart card technologies and co-authored an extensive survey of smart-card technologies published by Elsevier/Academic Press in 2004 (see Drew’s directory page above).
 I could tell from the many questions asked of the excellent presenters that there is a lot of misinformation out there on the different types of identity theft, the scope of people who commit this type of theft, the trends, and what we can do about better detecting and preventing this theft. Three blogs mentioned in their handout to help us keep up with the latest and greatest scams, schemes, and trends related to ID theft are:
I could tell from the many questions asked of the excellent presenters that there is a lot of misinformation out there on the different types of identity theft, the scope of people who commit this type of theft, the trends, and what we can do about better detecting and preventing this theft. Three blogs mentioned in their handout to help us keep up with the latest and greatest scams, schemes, and trends related to ID theft are:
FightIdentityTheft Blog — http://fightidentitytheft.com/blog
Schneier On Security — http://schneier.com/blog
Identity Theft Blog by Truston — http://www.mytruston.com/blog
I would like to add three of my favorite sites (also briefly mentioned in their handout) that I regularly use and direct interested people to for great information, found on my previously mentioned workshop website along with other related information, such as notable social networking sites, personal information search engines, and other online identity and privacy info sites:
Privacy Rights Clearinghouse — http://www.privacyrights.org/
Fighting Back Against Identity Theft — http://www.ftc.gov/bcp/edu/microsites/idtheft/
Identity Theft Resource Center — http://www.idtheftcenter.org/
OK, still not sure if you should care, or if the whole thing is even worth considering? If that is true, then my guess is that you did not look at any of the blogs or sites mentioned above, yet. At least try doing this–take the ID theft test and/or the PC info safety quiz from the Identity Theft Resource Center.
If you are not happy with your scores, then, reread this post and follow the links when you have some time to do something to help yourself and others. You will be glad that you did!
Remember, just as the experts will tell you, following your digital footprint and obtaining your personal info is easy to do if you are not aware, so easy even a caveman….well, you get the picture! 😉
-Robert Lackie
Technorati Tags: digital footprint, identity theft, online content, privacy conundrum, Library Garden
Making–and Protecting–your Digital Footprint: Do you Care? Even a Little Bit??
This weekend, the blogosphere and listservs were batting around two interesting reports: The Pew Internet & American Life Project’s “Digital Footprints” report, which was published this Sunday, and the New Media Consortium’s/EDUCAUSE Learning Initiative’s co-published future 2008 “Horizon Report,” which will be published in late January 2008 (a lot of people, though, are commenting on the report based on their wiki that they use to review, report, and refine their research oriented efforts, which is available now. Although I like skimming this wiki and seeing their Table of Contents and some details, I will wait for the published report–if interested, you can read about and browse the 2004-2007 Horizon Reports on this page.
For now, though, I decided to concentrate on the “Digital Footprints: Online identity management and search in the age of transparency” report, which did surprise me a bit with some of its findings. Here is a portion of their published summary on their site:
“Internet users are becoming more aware of their digital footprint; 47% have searched for information about themselves online, up from just 22% five years ago. However, few monitor their online presence with great regularity. Just 3% of self-searchers report that they make a regular habit of it and 74% have checked up on their digital footprints only once or twice.
Indeed, most internet users are not concerned about the amount of information available about them online, and most do not take steps to limit that information. Fully 60% of internet users say they are not worried about how much information is available about them online. Similarly, the majority of online adults (61%) do not feel compelled to limit the amount of information that can be found about them online.” [bold/emphasis is mine]
What surprised me was the section in the summary and report that stated that “Most internet users are not concerned about the amount of information available about them online, and most do not take steps to limit that information.” According to the “Summary of Findings” from the entire 50-page freely available PDF report, many of us (Internet users) are not concerned about online information on us—see my bolded statements above, which are also found on page ii, as well as four classified categories of online adults concerning this subject: “Confident Creatives (17%)” “Concerned and Careful (21%),” “Worried by the Wayside (18%),” and “Unfazed and Inactive (43%).” Interesting titles and descriptions, by the way–so I read on.
It is just that, ever since I starting doing seminars for school districts and libraries on social networking sites and personal information search engines, a great deal of interest seemed to be generated on not only finding out what was “out there” on them and their “kids” but also on what they could do to protect themselves and others. I constantly get asked about this topic, at just about any type of Internet workshop that I host or present. Maybe many who do ask about it do fall into the “Concerned and Careful,” but that would not seem correct to me, given the concern that I have witnessed concerning the protection of minors and the prevalence of identity theft articles. Remember, the report states that “Just 38% say they have taken steps to limit the amount of online information that is available about them.”
Although this does not seem right to me, I have to remember that they are only talking about “online adults,” and not my mother, for instance. I also do believe that the Pew Internet & American Life Project crew do a wonderful job of collecting their information and putting together their reports, but I am still curious…. We have a few thousand people who regularly visit us here at the Library Garden; How would you classify yourself using their four categories and their descriptions (see below). I would say that I fall into the “Confident Creatives”–the smallest of the groups (although my son would point out that I definitely don’t match the description of a “young adult”—those who most likely fall into this category, according to Pew / Internet).
Taken directly from page 30-31 of the report, see the four categories of online adults based on online footprint concern:
1) “Confident Creatives are the smallest of the four groups, comprising 17% of online adults. They say they do not worry about the availability of their online data, and actively upload content, but still take steps to limit their personal information. Young adults are most likely to fall into this group.
2) The Concerned and Careful fret about the personal information available about them online and take steps to proactively limit their own online data. One in five online adults (21%) fall into this category.
3) Despite being anxious about how much information is available about them, members of the Worried by the Wayside group do not actively limit their online information. This group contains 18% of online adults.
4) The Unfazed and Inactive group is the largest of the four groups—43% of online adults fall into this category. They neither worry about their personal information nor take steps to limit the amount of information that can be found out about them online.”
So, Library Gardeners and readers—what category best fits you, and what do you think about these findings? I guess I just think people online are more concerned with the making of and protection of their digital footprints, but it won’t be the first time that my experience differs with the results of a study or survey.
-Robert
Technorati Tags: digital footprint, online content, personal information, Pew Internet, privacy conundrum, Library Garden
Comments from Campus
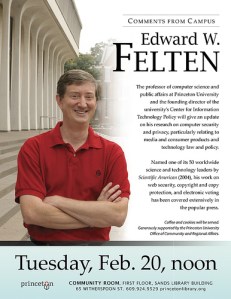 Two weeks ago Edward W. Felten was the first speaker in a new series called Comments from Campus — a collaboration between Princeton Public Library and Princeton University that endeavors to bring the campus to the community (or the gown to the town, if you will). We designed it as a lunch time brown bag lecture with the simple concept of inviting faculty to speak about a topic of their choosing and/or discuss their latest research in an informal setting. The topic is not settled beforehand as the idea is to give a platform for current research interests.
Two weeks ago Edward W. Felten was the first speaker in a new series called Comments from Campus — a collaboration between Princeton Public Library and Princeton University that endeavors to bring the campus to the community (or the gown to the town, if you will). We designed it as a lunch time brown bag lecture with the simple concept of inviting faculty to speak about a topic of their choosing and/or discuss their latest research in an informal setting. The topic is not settled beforehand as the idea is to give a platform for current research interests.
Unrolling a new program at a public library is nerve-wracking (as I have discovered since I took over as Program Coordinator here at PPL last fall). You are never sure if you will find the audience you are hoping to attract and doing this as a lunch lecture instead of an evening series was a bit of a risk. Our first talk was by all measures a great success and we had better than expected attendance — in large part to the speaker’s repuation, knowledge and also because of his choice of topic.
 Professor Felten delivered an entertaining and fascinating talk entitled “Real Policy for Virtual Worlds” where he examined a variety of interesting scenarios in which real world government or law may need to intervene in virtual worlds. Most of the 46 people in attendance had never even heard of Second Life or Norrath or any other virtual world before. You could see the look of amazement on several faces as they learned about the depth and breadth of virtual worlds. They were especially amazed to learn about Adam Reuters and Anshe Chung and how the Linden dollar can be traded like real currency. The talk was the perfect mix of technology and policy. I myself learned a lot, which was an added bonus because even though I have an avatar on Second Life I rarely spend time there. I have uploaded several photos from the talk on the PPL Flickr account if you would like to get a flavor of the talk — and a few of the other events that have been keeping me from blogging as often as I should.
Professor Felten delivered an entertaining and fascinating talk entitled “Real Policy for Virtual Worlds” where he examined a variety of interesting scenarios in which real world government or law may need to intervene in virtual worlds. Most of the 46 people in attendance had never even heard of Second Life or Norrath or any other virtual world before. You could see the look of amazement on several faces as they learned about the depth and breadth of virtual worlds. They were especially amazed to learn about Adam Reuters and Anshe Chung and how the Linden dollar can be traded like real currency. The talk was the perfect mix of technology and policy. I myself learned a lot, which was an added bonus because even though I have an avatar on Second Life I rarely spend time there. I have uploaded several photos from the talk on the PPL Flickr account if you would like to get a flavor of the talk — and a few of the other events that have been keeping me from blogging as often as I should.
On a side note, you might want to consider adding Felten’s always fascinating Freedom to Tinker to your blogroll — I have long been an avid reader and he always gives me food for thought.




